On this page
How to Enforce MFA on AWS for All IAM Users with Console Access
Introduction
If you’re still not using AWS Identity Center for access control on your AWS account then most likely you are stuck with the old IAM users pattern.
If you’re someone who hasn’t enabled MFA on the IAM users yet then you must do that immediately. Most of the security issues that we have seen on our customer sides have been either due to password leak of IAM users or due to access key leaks.
AWS provides several mechanisms to enforce MFA on IAM Users, but implementing them correctly requires understanding the intricacies of IAM policies, user experience considerations, and operational impacts. This guide provides a simple approach to enforce MFA across your AWS organization, addressing common implementation challenges and ensuring minimal disruption.
The implementation covers two key methods: policy-based enforcement, organizational controls. One approach is for enforcing the policy account level and the other is used by organisations to control MFA policies centrally for all AWS accounts managed under them using IAM Identity center.
Step-by-Step Implementation
Understanding MFA Enforcement Mechanisms
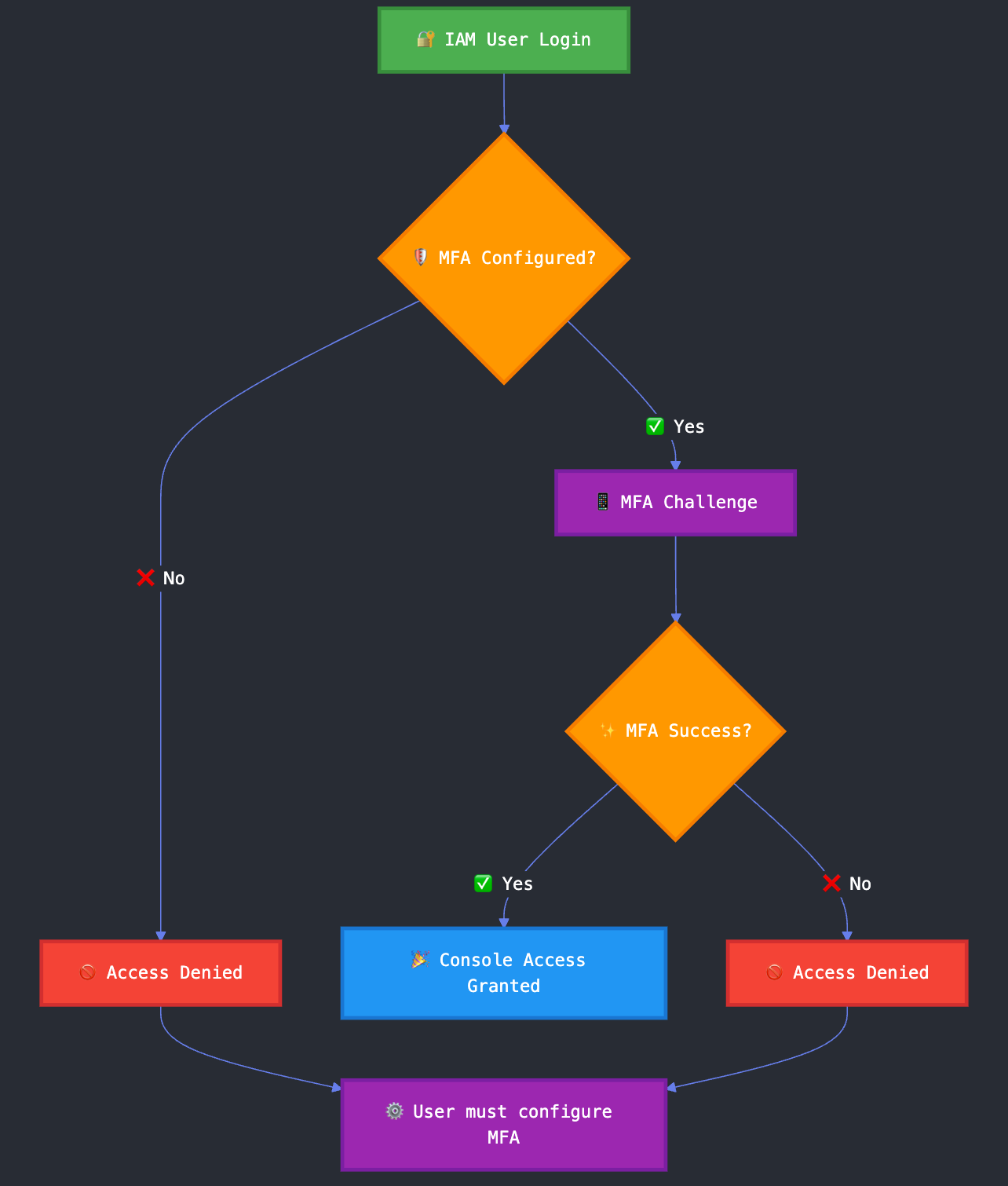
Method 1: IAM Policy-Based Enforcement
Create an IAM policy that denies all actions except MFA device management when MFA is not present.
This is the simplest approach to enforce MFA for all IAM users with console access. It involves creating the policy and attaching it to the users or groups that require MFA.
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "AllowViewAccountInfo",
"Effect": "Allow",
"Action": [
"iam:GetAccountPasswordPolicy",
"iam:GetAccountSummary",
"iam:ListVirtualMFADevices"
],
"Resource": "*"
},
{
"Sid": "AllowManageOwnPasswords",
"Effect": "Allow",
"Action": [
"iam:ChangePassword",
"iam:GetUser"
],
"Resource": "arn:aws:iam::*:user/${aws:username}"
},
{
"Sid": "AllowManageOwnMFA",
"Effect": "Allow",
"Action": [
"iam:CreateVirtualMFADevice",
"iam:DeleteVirtualMFADevice",
"iam:EnableMFADevice",
"iam:ListMFADevices",
"iam:ResyncMFADevice"
],
"Resource": [
"arn:aws:iam::*:mfa/${aws:username}",
"arn:aws:iam::*:user/${aws:username}"
]
},
{
"Sid": "DenyAllExceptUnlessSignedInWithMFA",
"Effect": "Deny",
"NotAction": [
"iam:CreateVirtualMFADevice",
"iam:EnableMFADevice",
"iam:GetUser",
"iam:ListMFADevices",
"iam:ListVirtualMFADevices",
"iam:ResyncMFADevice",
"sts:GetSessionToken"
],
"Resource": "*",
"Condition": {
"BoolIfExists": {
"aws:MultiFactorAuthPresent": "false"
}
}
}
]
}
Attach this policy to all users or groups that require console access:
# Create the policy
aws iam create-policy \
--policy-name EnforceMFA \
--policy-document file://enforce-mfa-policy.json
# Attach to a group
aws iam attach-group-policy \
--group-name ConsoleUsers \
--policy-arn arn:aws:iam::ACCOUNT-ID:policy/EnforceMFA
# Or attach to individual users
aws iam attach-user-policy \
--user-name username \
--policy-arn arn:aws:iam::ACCOUNT-ID:policy/EnforceMFA
Once the policy is attached, the user will not not be able to perform any actions on the console apart from managing their own MFA device. Once they have configured MFA, they will be able to perform all actions as per their IAM permissions.
Method 2: Organizations Service Control Policy (SCP)
For organizations managing multiple AWS accounts, use SCPs to enforce MFA at the organizational level.
This approach is only applicable for organizations that use IAM Identity Center and manage multiple AWS accounts under them.
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "DenyAccessWithoutMFA",
"Effect": "Deny",
"Action": "*",
"Resource": "*",
"Condition": {
"BoolIfExists": {
"aws:MultiFactorAuthPresent": "false"
},
"StringNotEquals": {
"aws:RequestedRegion": "us-east-1"
}
},
"Principal": {
"AWS": "*"
}
},
{
"Sid": "AllowMFAManagement",
"Effect": "Allow",
"Action": [
"iam:CreateVirtualMFADevice",
"iam:EnableMFADevice",
"iam:GetUser",
"iam:ListMFADevices",
"iam:ListVirtualMFADevices",
"iam:ResyncMFADevice",
"iam:ChangePassword",
"iam:GetAccountPasswordPolicy",
"iam:GetAccountSummary",
"sts:GetSessionToken"
],
"Resource": "*",
"Principal": {
"AWS": "*"
}
}
]
}
Apply the SCP to organizational units:
# Create SCP
aws organizations create-policy \
--name "EnforceMFA" \
--description "Enforce MFA for all console access" \
--type SERVICE_CONTROL_POLICY \
--content file://scp-enforce-mfa.json
# Attach to organizational unit
aws organizations attach-policy \
--policy-id p-xxxxxxxxx \
--target-id ou-xxxxxxxxx
Conclusion
Enforcing MFA for all IAM users with console access requires a systematic approach. It's very simple to implement but a lot of administrators still don't do it.
The investment in MFA enforcement pays significant dividends in reduced security risk and improved compliance posture. By implementing these controls, organizations can dramatically reduce their exposure to credential-based attacks.
For organizations requiring assistance with AWS security implementations, Kubenine's team of experienced DevOps consultants can help ensure proper configuration and ongoing management of MFA and other critical security controls. Our expertise in AWS security best practices enables us to implement robust authentication mechanisms for you. Contact us to learn how we can help strengthen your AWS security posture.

