On this page
How to Access Private Databases in AWS VPC (Bastion Host + SSH Tunnel Guide)
Struggling to connect to a private AWS database? Learn how bastion hosts and SSH tunneling enable secure access to databases inside a VPC.
Introduction
Your database is running inside a private AWS VPC.
No public IP. No direct access. Fully secure.
But now you need to:
- Debug an issue
- Run migrations
- Connect from your local machine
This is one of the most common real-world problems DevOps engineers face.
If you're also working on Kubernetes or observability, check the related guides at the end of this post.
In this guide, you will learn:
- How to access private databases using a bastion host
- How SSH tunneling works
- Secure alternatives like AWS SSM Session Manager
- Best practices used in production environments
AWS VPC Architecture for Private Database Access

AWS VPC bastion host architecture for accessing private databases securely
Architecture Breakdown
- The database runs inside a private subnet
- It has no public internet access
- A bastion host (EC2) sits in a public subnet
- You connect to bastion, and bastion connects to the database
This setup ensures secure and controlled access.
What is a Bastion Host
A bastion host is a publicly accessible EC2 instance used to access private resources inside a VPC.
Key responsibilities:
- Acts as a secure entry point
- Prevents direct exposure of the database
- Enables controlled SSH access
It serves as a gateway between your local machine and private infrastructure.
Step-by-Step: Access Private Database
1. Launch Bastion Host
- Create an EC2 instance in a public subnet
- Attach an Elastic IP
- Allow SSH (port 22) from your IP only
2. Configure Security Groups
AWS security group configuration for bastion host and private database access
Bastion Host:
- Allow inbound SSH from your IP
Database:
- Allow inbound traffic from the bastion host private IP
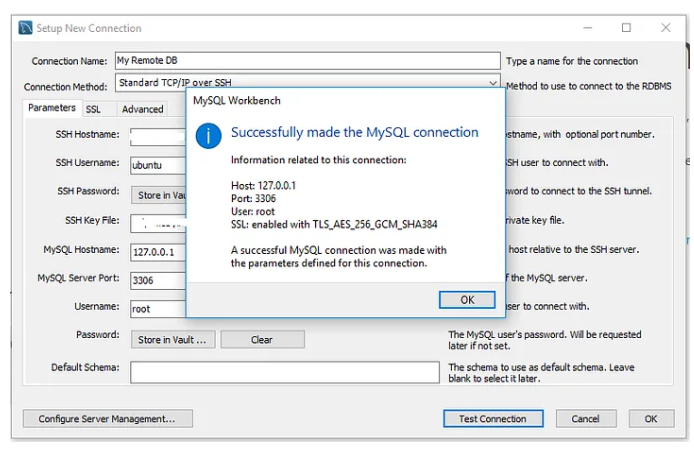
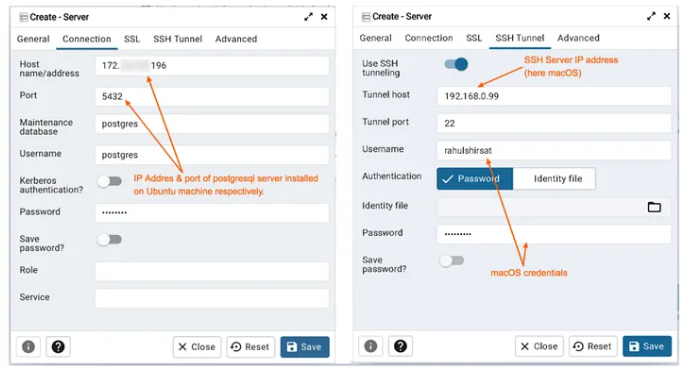
3. Create SSH Tunnel
Run the following command:
ssh -i your-key.pem -L 5432:your-db-endpoint:5432 ec2-user@bastion-ipThis creates an encrypted tunnel between your local machine and the database.
4. Connect to Database
Use:
localhost:5432You are now securely connected to the private database.
How SSH Tunneling Works
SSH tunneling flow from local machine to private database via bastion host
SSH tunneling forwards traffic securely from your local machine to the database through the bastion host.
- Local port to bastion host to database
- All traffic is encrypted
- Database remains private
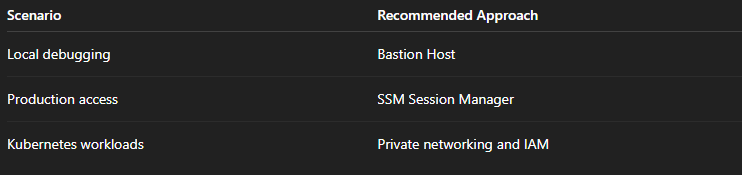
Bastion Host vs AWS SSM Session Manager
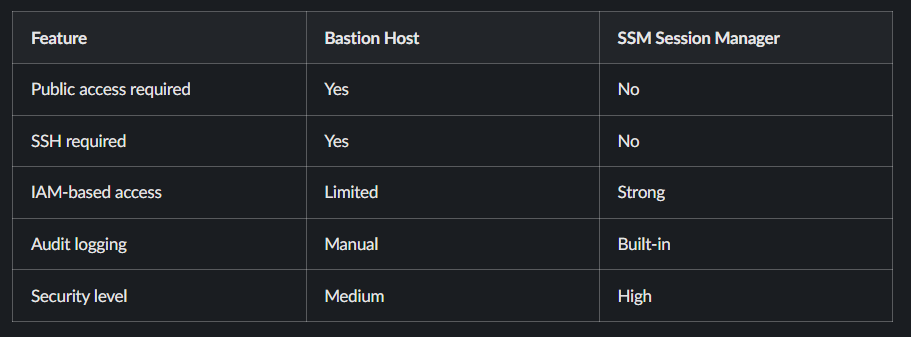
Recommendation:
- Use bastion host for quick debugging
- Use SSM Session Manager for production environments
Kubernetes Use Case: Accessing Private RDS
In Kubernetes environments, applications often need access to private databases.
Common approaches:
- VPC peering
- IAM roles for service accounts (IRSA)
- Private endpoints
- Sidecar proxies
Bastion hosts are not recommended for production Kubernetes workloads.
Security Best Practices
- Restrict SSH access to your IP only
- Rotate SSH keys regularly
- Use IAM roles instead of static credentials
- Enable logging using CloudWatch and VPC Flow Logs
- Avoid exposing databases publicly
Common Errors and Fixes
Connection Timeout
- Check security groups
- Verify subnet routing
SSH Tunnel Not Working
- Verify port forwarding
- Check database endpoint
Permission Denied
Fix:
chmod 400 your-key.pemWhen Should You Use What
Related Guides
If you're working with cloud infrastructure, Kubernetes, and DevOps tooling, these guides will help you go deeper:
- https://www.kubeblogs.com/alpine-vs-ubuntu-performance-network-speed/
- https://www.kubeblogs.com/fluent-bit-vs-grafana-alloy-kubernetes-observability-2026/
- https://www.kubeblogs.com/gcp-billing-kill-switch-terraform/
Conclusion
Accessing private databases in AWS VPC is both a technical challenge and a security requirement.
While bastion hosts are simple and effective, modern architectures are moving toward:
- IAM-based access
- Zero trust networking
- Private connectivity
Choose the approach based on your security requirements, team maturity, and infrastructure complexity.
Frequently Asked Questions
How do I access a private RDS instance from my local machine
Use a bastion host with SSH tunneling or AWS SSM Session Manager.
Is bastion host secure
It is secure if configured properly, but SSM Session Manager is more secure and recommended for production.
Can Kubernetes access private databases directly
Yes, using VPC networking, IAM roles, or private endpoints.
KubeNine Consulting helps teams design and implement CI/CD infrastructure for multi-cloud deployments. We've set up self-hosted runner architectures for organizations running hundreds of jobs per day across private infrastructure. Visit kubenine.com to learn how we can help streamline your build and deployment pipelines.

